#include "suricata-common.h"#include "suricata.h"#include "decode.h"#include "detect.h"#include "detect-engine.h"#include "detect-parse.h"#include "rust.h"#include "detect-asn1.h"#include "detect-content.h"#include "detect-pcre.h"#include "detect-isdataat.h"#include "detect-bytetest.h"#include "detect-bytemath.h"#include "detect-bytejump.h"#include "detect-byte-extract.h"#include "detect-entropy.h"#include "detect-replace.h"#include "detect-engine-content-inspection.h"#include "detect-uricontent.h"#include "detect-urilen.h"#include "detect-engine-uint.h"#include "detect-bsize.h"#include "detect-lua.h"#include "detect-base64-decode.h"#include "detect-base64-data.h"#include "detect-dataset.h"#include "detect-datarep.h"#include "util-spm.h"#include "util-debug.h"#include "util-print.h"#include "util-validate.h"#include "util-unittest.h"#include "util-unittest-helper.h"#include "util-profiling.h"#include "util-lua.h"#include "tests/detect-engine-content-inspection.c"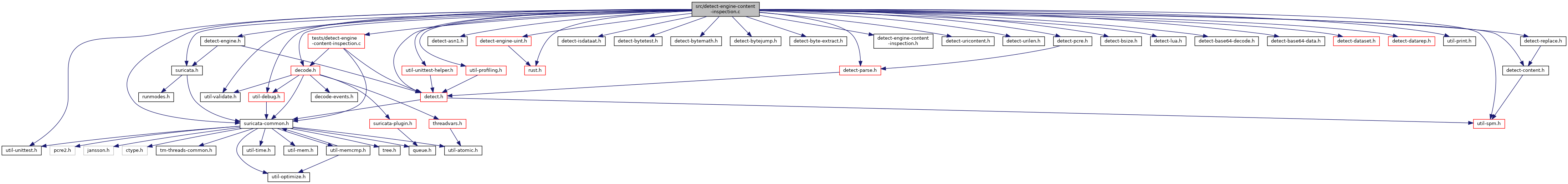
Go to the source code of this file.
Data Structures | |
| struct | DetectEngineContentInspectionCtx |
Functions | |
| bool | DetectEngineContentInspection (DetectEngineCtx *de_ctx, DetectEngineThreadCtx *det_ctx, const Signature *s, const SigMatchData *smd, Packet *p, Flow *f, const uint8_t *buffer, const uint32_t buffer_len, const uint64_t stream_start_offset, const uint8_t flags, const enum DetectContentInspectionType inspection_mode) |
| wrapper around DetectEngineContentInspectionInternal to return true/false only More... | |
| bool | DetectEngineContentInspectionBuffer (DetectEngineCtx *de_ctx, DetectEngineThreadCtx *det_ctx, const Signature *s, const SigMatchData *smd, Packet *p, Flow *f, const InspectionBuffer *b, const enum DetectContentInspectionType inspection_mode) |
| wrapper around DetectEngineContentInspectionInternal to return true/false only More... | |
| bool | DetectContentInspectionMatchOnAbsentBuffer (const SigMatchData *smd) |
| tells if we should match on absent buffer, because there is an absent keyword being used More... | |
Variables | |
| thread_local uint32_t | ut_inspection_recursion_counter = 0 |
Detailed Description
Performs content inspection on any buffer supplied.
Definition in file detect-engine-content-inspection.c.
Function Documentation
◆ DetectContentInspectionMatchOnAbsentBuffer()
| bool DetectContentInspectionMatchOnAbsentBuffer | ( | const SigMatchData * | smd | ) |
tells if we should match on absent buffer, because there is an absent keyword being used
- Parameters
-
smd array of content inspection matches
- Return values
-
bool true to match on absent buffer, false otherwise
Definition at line 789 of file detect-engine-content-inspection.c.
References DETECT_ABSENT, SigMatchData_::is_last, and SigMatchData_::type.
◆ DetectEngineContentInspection()
| bool DetectEngineContentInspection | ( | DetectEngineCtx * | de_ctx, |
| DetectEngineThreadCtx * | det_ctx, | ||
| const Signature * | s, | ||
| const SigMatchData * | smd, | ||
| Packet * | p, | ||
| Flow * | f, | ||
| const uint8_t * | buffer, | ||
| const uint32_t | buffer_len, | ||
| const uint64_t | stream_start_offset, | ||
| const uint8_t | flags, | ||
| const enum DetectContentInspectionType | inspection_mode | ||
| ) |
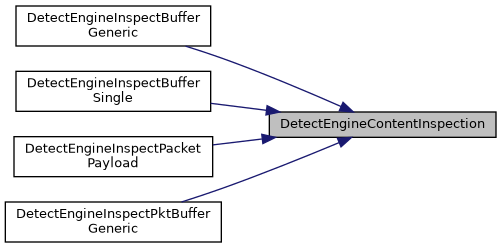
wrapper around DetectEngineContentInspectionInternal to return true/false only
- Parameters
-
smd sigmatches to evaluate
Definition at line 751 of file detect-engine-content-inspection.c.
References DetectEngineThreadCtx_::buffer_offset, ctx, de_ctx, and DetectEngineCtx_::inspection_recursion_limit.
Referenced by DetectEngineInspectBufferGeneric(), DetectEngineInspectBufferSingle(), DetectEngineInspectPacketPayload(), and DetectEngineInspectPktBufferGeneric().
◆ DetectEngineContentInspectionBuffer()
| bool DetectEngineContentInspectionBuffer | ( | DetectEngineCtx * | de_ctx, |
| DetectEngineThreadCtx * | det_ctx, | ||
| const Signature * | s, | ||
| const SigMatchData * | smd, | ||
| Packet * | p, | ||
| Flow * | f, | ||
| const InspectionBuffer * | b, | ||
| const enum DetectContentInspectionType | inspection_mode | ||
| ) |
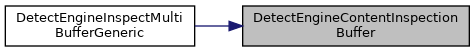
wrapper around DetectEngineContentInspectionInternal to return true/false only
content inspect entry for inspection buffers
- Parameters
-
smd sigmatches to evaluate
Definition at line 772 of file detect-engine-content-inspection.c.
References DetectEngineThreadCtx_::buffer_offset, ctx, de_ctx, and DetectEngineCtx_::inspection_recursion_limit.
Referenced by DetectEngineInspectMultiBufferGeneric().
Variable Documentation
◆ ut_inspection_recursion_counter
| thread_local uint32_t ut_inspection_recursion_counter = 0 |
Definition at line 69 of file detect-engine-content-inspection.c.
